
IDENTITY-BASED SIGNCRYPTION WITHOUT
RANDOM ORACLES
Shivaramakrishnan Narayan, Parampalli Udaya and Peter Hyun-Jeen Lee
Department of Computer Science and Software Engineering
University of Melbourne, Victoria - 3010, Australia
Keywords:
Identity based Cryptography, Bilinear Maps, Signcryption, Standard Model.
Abstract:
The use of signcryption for secure and authenticated data communication was realized in 1997, following
which numerous signcryptions have been presented which are provably secure in the random oracle proof
methodology. In this paper, we present an identity-based signcryption provably secure in the standard model.
Our scheme relies on the intractability of two well studied problems, the decisional bilinear Diffie-Hellman
and the computational Diffie-Hellman. We achieve the security reduction of our scheme for the properties
message confidentiality and unforgeability without relying on random oracles.
1 INTRODUCTION
A generic approach to achieve message authentica-
tion and confidentiality is by signing and encrypting
the message sequentially. Apparently, this generic
approach is a part of folkfore and commonly used
by practioners. Initially, this way of achieving both
authenticity and confidentiality was presented by
Stallings (Stallings, 1999) with respect to symmet-
ric key cryptography. In public key context, Zheng
proposed a new primitive known as signcryption to
achieve message confidentiality and authenticity si-
multaneously at a (computational and communica-
tional) cost less than the generic approach (Zheng,
1997). Since the revival of identity-based cryptogra-
phy in 2001 several identity-based signcryptions have
been proposed. In this paper, we present an identity-
based signcryption in the standard model.
The importance of security proof was realized in
the early 90’s. Since then a cryptographic scheme and
its property is evaluated based on the proof outlining
the reduction of the scheme to its underlying math-
ematical hard problem. Most of the identity-based
signcryptions defined in the literature (Libert and
Quisquater, 2003; McCullagh and Barreto, 2004; Lib-
ert and Quisquater, 2004; Malone-Lee, 2002; Chen
and Malone-Lee, 2004; Yuen and Wei, 2004; Boyen,
2003; Barreto et al., 2005) are proved secure in a prac-
tice oriented proof methodology introduced by Bel-
lare and Rogaway in 1993. This proving technique is
known as the “Random Oracle Model” (Bellare and
Rogaway, 1993). Although a stronger proof model
namely the “Standard Model” was known to the com-
munity, efficient schemes in the standard model were
not constructed due to the difficulty in presenting the
security reduction.
Identity-based Encryption in Standard Model.
The first efficient identity-based encryption provably
secure without random oracles was defined by Boneh
and Boyen (Boneh and Boyen, 2004) in 2004. Al-
though the scheme was proved secure in a slightly
weaker notion in which an adversary has to commit
to a public identity (challenge identity used in the at-
tack game) in advance. Following the result of Boneh
and Boyen, Waters defined the first identity-based en-
cryption which is fully secure without random ora-
cles (Waters, 2005). His work was inspired by the
hierarchical encryption scheme presented by Boneh
and Boyen (Boneh-Boyen presented two encryption
schemes in (Boneh and Boyen, 2004)). The way iden-
tity is mapped to a public key in Waters encryption
scheme is based on a collison-resistant function given
by Boneh and Boyen in (Boneh and Boyen, 2004).
The Waters scheme is based on strong, well-studied
problem namely decisional bilinear Diffie-Hellman.
Recently, a practical identity-based encryption in the
standard model with compact public parameter length
was presented in the paper (Gentry, 2006). But, the
scheme is based on a strong assumption known as au-
gumented bilinear Diffie-Hellman exponent problem.
342
Narayan S., Udaya P. and Hyun-Jeen Lee P. (2008).
IDENTITY-BASED SIGNCRYPTION WITHOUT RANDOM ORACLES.
In Proceedings of the International Conference on Security and Cryptography, pages 342-347
DOI: 10.5220/0001929603420347
Copyright
c
SciTePress

Identity-based Signature in Standard Model.
One can construct simple IBS schemes by using or-
dinary signature scheme in the standard model by at-
taching a certificate containing the public key of the
signer. Many such simple schemes have been men-
tioned in the literature, for example see (Gentry and
Silverberg, 2002; Kiltz et al., 2005; Dodis et al.,
2003). However these signatures have disadvantages
from two counts: they are computationally expen-
sive (two sign verifications) and secondly, they have a
large signature space (need to include the public key
of the signer and two signatures (one by the signer and
the other by the certifier)). The first direct construc-
tion of efficient ID-based signature in the standard
model was presented by Paterson and Schuldt (Pater-
son and Schuldt, 2006). The signature is based on the
hierarchical extension of Waters encryption scheme
(Waters, 2005). This methodology of converting a 2-
level hierarchical Identity-Based Encryption (HIBE)
to an IBS scheme was first presented by Gentry and
Silverberg (Gentry and Silverberg, 2002).
Identity-based Signcryption in Standard Model.
The construction of signcryption primitive poses two
main problems. Firstly, the computational and space
complexities of the primitive should be smaller than
the combined complexities of encryption and signa-
ture. The space complexity is mainly responsible for
the runtime communication cost which includes the
amount of signcrypted data from a sender to a re-
ceiver. Secondly, the signcryption should admit for-
mal proofs in strong security model. We describe
such a strong model in Section 3.
In 2005, Yuen and Wei (Yuen and Wei, 2005) pre-
sented the first hierarchical signcryption in the stan-
dard model as an extension of their hierarchical sig-
nature construction. The security of their scheme is
based on weaker notion called sample identity. This
notion is weaker than the selective identity model,
where the challenge identity is chosen by the adver-
sary before the start of the game. The signcryption re-
quires 7 pairings (1 pre-computable) and 9 exponen-
tiations. Our goal is to present an efficient identity-
based signcryption which is provably secure in the
standard model where adversary can change chal-
lenge identity adaptively.
Signcryption is primarily useful in applications
where secure and authenticated data transmission is
necessary at a low computational and communica-
tional cost. Another application where signcryptions
are useful is in the area of key establishment proto-
cols. In key establishment protocols authenticity and
confidentiality need to be simultaneously satisfied for
the exchanged keys and hence the signcryption meets
this requirement perfectly. A basic signcryption is
equivalent to a one-pass key exchange if the message
block is viewed as the session key exchanged between
the users. An interesting observation from (Gorantla
et al., 2007)states that the security notions of the sign-
cryption can be extended to key establishment proto-
cols. The security of key exchange protocols is based
on the indistinguishability of the keys by an adversary
and this notion is analogous to the indistinguishability
of ciphertext notion used in the signcryption security
model. The authenticity of the key exchanged fol-
lows from the message confidentiality notion of the
signcryption.
1.1 Our Contributions
Signcryption can be applied in two ways given a
message, sign and encrypt the message or encrypt
the message and sign. By following the latter ap-
proach we achieve public verifiability of the signa-
ture and the former way of signcryption results in
a non-public verifiable signature. In this paper, we
present a public verifiable identity-based signcryp-
tion in the standard model. Our construction is based
on Waters encryption and our efficient identity-based
signature. The security of the signcryption is based
on two well studied hard problems namely, the de-
cisional bilinear Diffie-Hellman and computational
Diffie-Hellman. Our scheme is secure in the adaptive
security notion defined in the Section 3. The scheme
performs better than serially combining any known
identity-based encryption and a signature in the stan-
dard model. We achieve reduction in the public pa-
rameter size, the signcryption size and the number of
exponentiations. The efficiency results are presented
in Table 1, Section 4.1. Further, it is to be noted that
there is no gain in the number of pairing operations
and the size of public parameter is same as in the Wa-
ters encryption scheme (Waters, 2005).
One of the disadvantages of schemes based on
Waters hash is that the public parameters space is
large. We have been able to reduce the public param-
eters space by half to that of Paterson-Schuldt scheme
(Paterson and Schuldt, 2006). However, it should be
pointed out that the public parameters are acquired
only for the initialization of the scheme and does not
affect runtime cost of signcrypted data. The initial-
ization requirements can be easily accomplished in a
desktop environment and thereby, the practicality of
the scheme should not be affected.
IDENTITY-BASED SIGNCRYPTION WITHOUT RANDOM ORACLES
343

1.2 Paper Outline
In Section 2, we present the necessary mathematical
preliminaries and the related complexity assumptions.
The security model for our signcryption is detailed in
Section 3, followed by our signcryption construction
and its efficiency in Section 4. Section 5 presents a
detailed proof of our scheme and finally, Section 6
presents our conclusion.
2 BACKGROUND
Before we describe the construction of our scheme,
we present a brief overview of the notations and other
basic mathematical assumptions followed in the pa-
per.
2.1 Bilinear Maps
Let G
1
and G
2
be multiplicative groups of prime
order q. Let Z
∗
q
denote the set of all non-zero in-
tegers modulo prime q. A bilinear map is a map
ˆe : G
1
×G
1
→ G
2
, satisfying the following properties.
- ˆe is bilinear, i.e. for all g,g
1
,g
2
∈ G
1
and a,b ∈
Z
∗
q
, we have
(a) ˆe(g,g
1
· g
2
) = ˆe(g,g
1
) · ˆe(g,g
2
).
(b) ˆe(g
a
,g
b
1
) = ˆe(g,g
1
)
ab
= ˆe(g
b
,g
a
1
).
- ˆe is non-degenerate, i.e. for g ∈ G
1
/1, ˆe(g,g) 6= 1.
- ˆe is efficiently computable.
2.2 Admissible Collision-resistant
Functions
Our scheme uses collision resistant function of the
form {0,1}
n
u
−→ G
1
, where n
u
denotes the length of
an identity and can constructed as given in (Waters,
2005). In addition, we use a target collision resis-
tant function of the nature G
2
× G
1
−→ Z
∗
q
, this can
be constructed using general cryptographichash func-
tions. To allowidentities of arbitrary length, collision-
resistant hash function, H
1
: {0,1}
∗
−→ {0, 1}
n
u
can
be defined.
2.3 Identity-based Signcryption
An identity-based signcryption consists of the follow-
ing four algorithms.
Set-up. Given a security parameter k, this algorithm
generates the global public parameters params
and the master secret. The private key generator
keeps the master secret to itself and publishes the
global public parameters params.
Extract. Given a user’s identity ID, the algorithm
generates the private key d
ID
of ID using the mas-
ter secret and params. The private key generator
will use this algorithm to generate the private key
of all the users participating in the scheme.
Signcrypt. Given a message M, a receiver’s identity
ID
R
and the private key d
ID
S
of a sender ID
S
, this
algorithm outputs a signcrypted text of the mes-
sage M.
Unsigncrypt. Given a signcrypted text, public key
of the sender ID
S
and private key of the receiver
d
ID
R
, this algorithm outputs the message M if the
signcrypted text is valid, else returns ⊥.
2.4 Complexity Assumptions
2.4.1 Computational Diffie-Hellman Problem
Given (g,g
a
,g
b
) ∈ G
1
, where g is a generator of G
1
and a, b∈ Z
∗
q
, the computationalDiffie-Hellman prob-
lem is to compute g
ab
.
2.4.2 Decisional Bilinear Diffie-Hellman
(DBDH) Problem
Given (g,g
a
,g
b
,g
c
,Y) ∈ G
4
1
× G
2
, where g is a gener-
ator of G
1
, Y ∈ G
2
and a, b,c ∈ Z
∗
q
, the DBDH prob-
lem is to determine if Y = ˆe(g,g)
abc
.
2.5
teste
3 SECURITY NOTIONS FOR
S
IGNCRYPTION
The signcryption scheme we present is proved under
the adaptive identity model for both indistinguisha-
bility and existential unforgeability attacks. A brief
description of the game in given below.
3.0.1 Indistinguishability of Chosen Ciphertext
Definition 3.0.1. We say that an Id-based sign-
cryption scheme (IDSC) has the indistinguishabil-
ity against adaptive identity chosen ciphertext at-
tack property (IND-IDSC-CCA2), if no polynomially
bounded adversary has a non-negligible advantage in
the following attack game.
Setup. The challenger runs the Setup() algorithm of
the scheme and sends the global system parameter
to the adversary A .
SECRYPT 2008 - International Conference on Security and Cryptography
344

Phase 1. A performs polynomially bounded number
of queries as follows:
- Extract Query: The adversary submits an iden-
tity ID to the challenger. The challenger runs
the Extract() algorithm and responds with the
private key of ID.
- Signcrypt Query: The adversary submits a
sender identity, receiver identity and message
to the challenger. The challenger runs the Sign-
crypt() algorithm and responds with the sign-
cryption of the message consisting of the sig-
nature processed with private key of the sender,
and encryption of the given message using pub-
lic key of the receiver.
- Unsigncrypt Query: The adversary submits a
sender identity, a receiver identity and a sign-
crypted text to the challenger. The challenger
runs the Unsigncrypt() algorithm and returns
the output.
Challenge. Once the adversary decides that Phase
1 is over, it presents two equal length messages
M
0
,M
1
, sender’s identity ID
∗
1
and a recipient iden-
tity ID
∗
2
on which it wishes to be challenged for
which adversary did not ask the private key. The
challenger chooses a random bit b and computes
the signcryption of the message M
b
and sends the
signcrypted message to the adversary.
Phase 2. The adversary continues to probe the chal-
lenger with additional queries as in Phase 1. It is
not allowed to extract the private key correspond-
ing to the challenged identity ID
∗
2
.
Response. The adversary outputs a bit b
′
∈ {0, 1}
and wins the game if b
′
= b.
Definition 3.0.2. An adversary (ε,Q
e
,Q
s
)-A against
IND-IDSC-CCA2 exists if A that makes makes at most
Q
e
extract queries and Q
s
signcryption queries has an
advantage at least ε in the above game. A scheme
is said to be (ε,Q
e
,Q
s
)-secure if no (ε,Q
e
,Q
s
)-
adversary exists.
3.0.2 Existential Unforgeability
Definition 3.0.3. We say that an Id-based signcryp-
tion scheme (IDSC) has existential unforgeability
property against adaptive identity chosen-message
attack or (EUF-IDSC-CMA), if no polynomially
bounded adversary A has a non-negligible advantage
in the following attack game.
Setup. The challenger runs the Setup() algorithm of
the scheme and sends the global system parameter
to the adversary A .
Phase 1. A performs polynomially bounded number
of queries as in the above game.
Forge. The adversary chooses a sender’s identity
ID
∗
1
, receiver identity ID
∗
2
as the challenge identi-
ties and returns signature forgery Z on a message
M.
Response. The adversary wins if ID
i
6= ID
∗
1
, ID
∗
1
6=
ID
∗
2
and Unsigncrypt(Z, M,ID
∗
2
) = ⊤. The ad-
versary should not have made extract query on
ID
∗
1
and ID
∗
2
, and the forgery did not result
from a query made to Signcrypt algorithm using
(M,ID
∗
1
,ID
∗
2
).
The adversary’s advantage is defined to be Adv(A ) =
Pr[A wins].
Definition 3.0.4. An adversary A is said to be
an (ε,Q
e
,Q
s
)-forger of an IDSC scheme if A that
makes at most Q
e
extract queries and Q
s
signcryp-
tion queries has an advantage at least ε in the above
game. A scheme is said to be (ε,Q
e
,Q
s
)-secure if no
(ε,Q
e
,Q
s
)-forger exists.
4 NEW IDENTITY-BASED
SIGNCRYPTION (IDSC)
CONSTRUCTION
In this section, a new signcryption construction based
on an efficient signature construction is presented.
Setup. The private key generator (PKG) chooses
groups G
1
and G
2
of prime order q such that a bi-
linear map ˆe : G
1
× G
1
−→ G
2
can be constructed
and picks a generator g of G
1
. The PKG then se-
lects a secret s ∈ Z
∗
q
randomly, computes g
1
=
g
s
and picks g
2
∈
R
G
1
. Further, PKG chooses
u
′
,u
′
m
∈
R
G
1
and a vector
→
U
= (u
i
) of length n
u
whose entries are random elements from G
1
.
Given an identity u, V ⊆ {1,.....n
u
} denotes the
set of all i’s such that u[i] = 1, where u[i] is the
ith bit of the identity string. The public key g
u
is
calculated as given below.
g
u
= u
′
∏
i∈V
u
i
.
Given a string M
′′
, M ⊆ {1,.....n
m
′
} (where n
m
′
=
n
u
) denotes the set of all j’s such that M
′′
[ j] = 1
where, M
′′
[ j] is the jth bit of the string. g
m
′′
is
calculated as follows.
H
m
′′
: g
m
′′
= u
′
m
∏
j∈M
u
j
.
In addition to H
u
, the PKG selects another target-
collision resistant function H
m
: G
2
× G
1
−→ Z
∗
q
to map the encrypted message.
IDENTITY-BASED SIGNCRYPTION WITHOUT RANDOM ORACLES
345
The public parameters of the system are
params =
g,g
1
,g
2
,u
′
,
→
U
,H
u
,H
m
and the mas-
ter secret is g
s
2
.
Extract. Given an identity ID, the private key d
ID
is
constructed as given below:
1. Choose r
ID
∈
R
Z
∗
q
.
2. The private key is d
ID
= (g
s
2
· (g
ID
)
r
ID
, g
r
ID
)
where, g
ID
= H
u
(ID).
Signcrypt. Given a message M, a sender identity A
and a receiver identity B, the signcryption on M is
constructed as follows.
1. Select t
1
,t
2
∈
R
Z
∗
q
.
2. Compute C = ˆe(g
1
, g
2
)
t
2
· M.
3. Compute M
′
= H
m
(C,W) where, W = g
r
A
+t
1
.
4. Let M
′′
be the binary representation of M
′
,
compute H
m
′
, g
M
′′
= u
′
m
∏
j∈M
u
j
, where M ⊆
{1,.....n
m
′
} denotes the set of all j’s such that
M
′′
[ j] = 1, M
′′
[ j] is the jth bit of the string.
5. Compute the value Z = g
t
1
A
(g
A
g
M
′′
)
M
′
t
2
·g
s
2
·g
r
A
A
.
6. The resulting signcryption is:
C, Z,U = g
t
2
,V = g
t
2
B
,W
.
UnSigncrypt. Given a signcryption (C, Z,U,V,W)
on message M, the unsigncryptionsteps are as fol-
lows:
1. Obtain the private key d
B
.
2. Compute M = C·
ˆe(g
r
B
, V)
ˆe(g
s
2
·(g
B
)
r
B
, U)
.
3. Compute M
′
= H
m
(C,W).
4. Let M
′′
be the binary representation of M
′
,
compute H
m
′
, g
M
′′
= u
′
m
∏
j∈M
u
j
, where M ⊆
{1,.....n
m
′
} denotes the set of all j’s such that
M
′′
[ j] = 1, M
′′
[ j] is the jth bit of the message
string.
5. Accept M if,
ˆe(Z,g) = ˆe(g
1
,g
2
) ˆe(W,g
A
) ˆe(U, (g
M
′′
g
A
)
M
′
).
4.1 Efficiency of IDSC
Table 1 gives a comparison of the computations in-
volved in our IDSC with respect to a generic sign-
cryption derivable using Waters encryption (Waters,
2005) and the signature presented by Paterson and
Schuldt (Paterson and Schuldt, 2006). In addition to
the computations, the signcryption size and the public
parameter size are mentioned. In case of the cipher-
text space, there is a reduction of one element over
G
1
. But again, due to the fact that W = g
r
A
+t
1
can be
fixed, a user needs to send this value only to a new re-
ceiver. This would further reduce the ciphertext space
by one element over G
1
. The public parameter size is
G
4
1
× G
n
u
1
.
The parameters n
u
and n
m
in Table 1 denotes the
length of an identity and a message respectively.
5 SECURITY PROOFS
In this section, security results of IDSC against
(ε,Q
e
,Q
s
)-IND-IDSC-CCA2 and (ε,Q
e
,Q
s
)-EUF-
IDSC-CMA attacks explained in Section 3 are pre-
sented. The proofs will appear in an extended paper.
The use of collision resistant function H
m
presents
the necessity of including the probability of collisions
which can affect the output of the attack game.
Theorem 5.0.1. Let H
m
be a target collision re-
sistant hash function used in our signcryption and
Adv
hash−tcr
TCR,H
(k) denote the advantage of an adversary
H against the collision resistance of H
m
. If there ex-
ists an adversary (ε,Q
e
,Q
s
)-A making at most Q
e
ex-
tract queries and Q
s
signcryption queries that suc-
ceeds against the IND-IDSC-CCA2 security of IDSC
with a probability ε, then there exists a challenger
B running in polynomial time that solves the DBDH
problem with a probability ε
′
at least
1
16(n
u
+ 1)(Q
e
+ Q
s
)
(1− Adv
hash−tcr
TCR,H
(k)).
Theorem 5.0.2. Let H
m
be a target collision resis-
tant hash function used in our signcryption scheme
and Adv
hash−tcr
TCR,H
(k) denote the advantage of an ad-
versary H against the collision resistance of H
m
. If
there is an (ε,Q
e
,Q
s
)-adversary A making at most Q
e
extract queries and Q
s
signcryption queries that suc-
ceeds against the EUF-IDSC-CMA security of IDSC
with a probability ε, then there exists a challenger B
running in polynomial time that solves the CDH prob-
lem with a probability ε
′
at least
ε
4(Q
e
+ Q
s
)
2
(n
u
+ 1)
(1− Adv
hash−tcr
TCR,H
(k)).
6 CONCLUSIONS
In this paper, we presented an efficient and fully
secure identity-based signcryption in the standard
model. The scheme presented is proved secure in
a well-defined adaptive identity chosen ciphertext
and chosen message attack security notions. The
scheme performs better than sequentially combining
any known identity-based encryption and a signature
in the standard model. We achieve reduction in the
SECRYPT 2008 - International Conference on Security and Cryptography
346
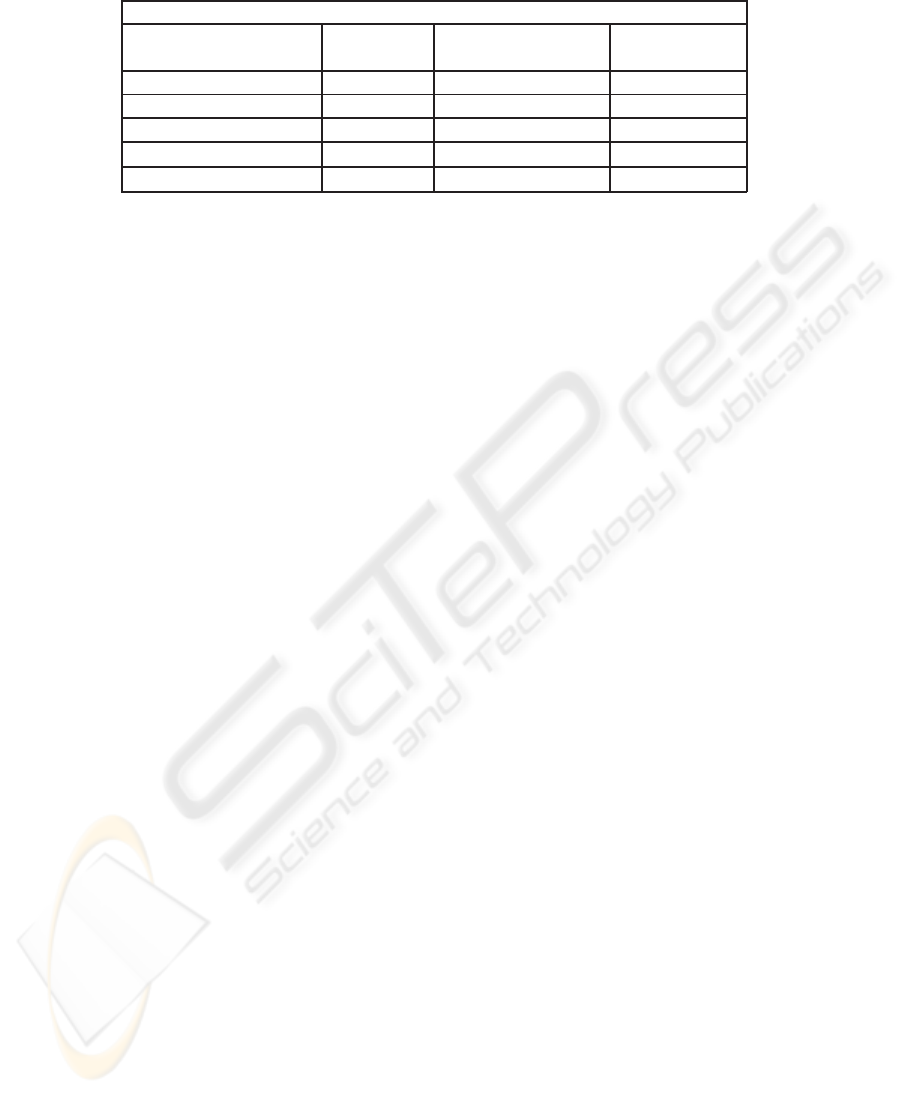
Table 1: Efficiency of IDSC.
PC - Denotes Pre-Computable
Waters Kenny and Schuldt Our
Encryption Signature Signcryption*
Pairings 3(1PC) 4(1PC) 7(2PC)
G
1
Exponentiations 2 3 3
G
2
Exponentiations 1 - 1
Signcryption Size G
2
× G
2
1
G
3
1
G
2
× G
4
1
Public Parameter Size G
4
1
× G
n
u
1
G
5
1
× G
n
u
1
× G
n
m
1
G
4
1
× G
n
u
1
public parameter size, signcryption size and exponen-
tiations. One of the shortcomings of our scheme is
its public parameter size. An open problem is to con-
struct a signcryption with compact public parameter
size.
REFERENCES
Barreto, P., Libert, B., McCullagh, N., and Quisquater, J.
(2005). Efficient and provably-secure identity-based
signatures and signcryption from bilinear maps. In
Advances in cryptology (ASIACRYPT 2005) (11th in-
ternational conference on the theory and application
of cryptology and information security), volume 3788,
pages 515–532. Lecture notes in computer science,
Springer, Berlin, ALLEMAGNE.
Bellare, M. and Rogaway, P. (1993). Random oracles are
practical:a paradigm for designing efficient protocols.
First ACM Conference on Computer and Communica-
tions Security, ACM, pages 62–72.
Boneh, D. and Boyen, X. (2004). Efficient selective-ID
secure identity based encryption without random or-
acles. In Advances in Cryptology EUROCRYPT 2004,
volume 3027, pages 223–238. Lecture Notes in Com-
puter Science, Springer Berlin/Heidelberg.
Boyen, X. (2003). Multipurpose identity-based signcryp-
tion: A swiss army knife for identity-based cryptogra-
phy. In Proceedings of Crypto 2003, 2729:383–399.
Chen, L. and Malone-Lee, J. (2004). Improved identity-
based sincryption. Cryptology ePrint Archive, Report
2004/114, 2004, http://eprint.iacr.org/2004/114/.
Dodis, Y., Katz, J., Xu, S., and Yung, M. (2003). Strong
key-insulated signature schemes. In Public Key Cryp-
tography - PKC 2003: 6th International Workshop on
Practice and Theory in Public Key Cryptography Mi-
ami, volume 2567, pages 130–144. Lecture notes in
computer science, Springer, Berlin, ALLEMAGNE.
Gentry, C. (2006). Practical identity-based encryption with-
out random oracles. In the Proceedings of Eurocrypt-
06, 4004:445–464.
Gentry, C. and Silverberg, A. (2002). Hierarchical ID-based
cryptography,. In Y. Zheng, editor, ASIACRYPT 2002,
volume 2501, pages 548–566. Lecture notes in com-
puter science, Springer, Berlin, ALLEMAGNE.
Gorantla, M., Boyd, C., and Gonzalez, J. (2007). On the
connection between signcryption and one-pass key
establishment. In Eleventh IMA International Con-
ference on Cryptography and Coding, To appear.
Springer.
Kiltz, E., Mityagin, A., Panjwani, S., and Raghavan, B.
(2005). Append-only signatures. In L. Caires, G.
F. Italiano, L. Monteiro, C. Palamidessi, and M.
Yung, editors, ICALP, volume 3580, pages 434–445.
Lecture notes in computer science, Springer, Berlin,
ALLEMAGNE.
Libert, B. and Quisquater, J. (2003). New identity-based
signcryption schemes from pairings. In IEEE Infor-
mation Theory Workshop, 2003, pages 155–158.
Libert, B. and Quisquater, J. (2004). Efficient signcryp-
tion with key privacy from gap Diffie-Hellman groups.
In In Public Key Cryptography - PKC 2004, volume
2947, pages 187–200. Lecture Notes in Computer Sci-
ence, Springer- Verlag.
Malone-Lee, J. (2002). Identity-based signcryption. IACR
eprint, report 2002/098.
McCullagh, N. and Barreto, P. (2004). Efficient and
forward-secure identity based signcryption. Cryptol-
ogy ePrint Archive, Report 2004/117.
Paterson, K. and Schuldt, J. (2006). Efficient identity-based
signatures secure in the standard model. ACISP 2006,
4058:207–222.
Stallings, W. (1999). Cryptography and Network Security
(2nd ed.): Principles and Practice. Prentice-Hall,
Inc., Upper Saddle River, NJ, USA.
Waters, B. (2005). Efficient identity based encryption
without random oracles. In Advances in Cryptology-
EUROCRYPT 2005, 3494:114–127.
Yuen, T. and Wei, V. (2004). Fast and proven secure blind
identity-based signcryption from pairings. Cryptology
ePrint Archive, Report 2004/121.
Yuen, T. and Wei, V. (2005). Constant-size hierarchical
identity-based signature/signcryption without random
oracles. Cryptology ePrint Archive, Report 2005/412,
http://eprint.iacr.org/.
Zheng, Y. (1997). Digital signcryption or how to achieve
cost(signature & encryption) <<cost(signature) +
cost(encryption). In Advances in Cryptology -
CRYPTO 97, 1294.
IDENTITY-BASED SIGNCRYPTION WITHOUT RANDOM ORACLES
347
