
WATERMARKING IMAGES USING 2D REPRESENTATIONS
OF SELF-INVERTING PERMUTATIONS
Maria Chroni, Angelos Fylakis and Stavros D. Nikolopoulos
Department of Computer Science, University of Ioannina, GR-45110 Ioannina, Greece
Keywords:
Watermarking Techniques, Image Watermarking Systems, Intellectual Property Rights, Color Images,
Self-inverting Permutations, 2D-representations of Permutations, Encoding, Decoding, Algorithms.
Abstract:
In this work we propose an efficient and easily implemented codec system, which we named WaterIMAGE,
for watermarking images that are intended for uploading on the web and making them public online. An
important fact of our system is that it suggests a way in which an integer number can be represented in a two
dimensional grid and, thus, since images are two dimensional objects that representation can be efficiently
marked on them. In particular, our system uses an efficient technique which is based on a 2D representation of
self-inverting permutations and mainly consists of two components: the first component contains an encoding
algorithm which encodes an integer w into a self-inverting permutation π
∗
and a decoding algorithm which
extracts the integer w from π
∗
, while the second component contains codec algorithms which are responsible
for embedding a watermark into an image I, resulting the image I
w
, and extract it from I
w
. Our system
incorporates important properties which allow us to successfully extract the watermark w from the image I
w
even if the input image has been compressed with a lossy method and/or rotated. All the system’s algorithms
have been developed and tested in JAVA programming environment.
1 INTRODUCTION
Internet technology, becomes day by day an indis-
pensable tool for everyday life since most people use
it on a regular basis and do many daily activities on-
line (Garfinkel, 2001). As a consequence, transferring
digital informationvia the Internet, such as audio, pic-
tures, video, or software, has also become very popu-
lar during the last years.This frequent use of internet
means that measures taken for internet security are
indispensable since the web is not risk-free. One of
those risks is the fact that the web is an environment
where intellectual property is under threat.And that’s
where watermarks come to place.
Watermarking. Watermarks are symbols which are
placed into physical objects such as documents, pho-
tos and bank notes and their purpose is to carry in-
formation about an object’s authenticity. In our case
the watermarks have digital form and they are embed-
ded into digital objects, this technique is called digital
watermarking.
The watermarking problem can be described as
the problem of embedding a watermark w into an ob-
ject I and, thus, producing a new object I
w
, such that
w can be reliably located and extracted from I
w
even
after I
w
has been subjected to transformations (Coll-
berg and Nagra, 2010); for example, compression in
case the object is an image.
Motivation. We believe that protecting intellectual
material on the web is one of the major issues con-
cerning the proper use of the internet. Digital images
are a very characteristic part of this material found
online and our target is to make people feel free to
upload their images without hesitating because of the
fear of their work being unauthorized used.
Watermarking is the ideal solution for protecting
your property of the images and keeping them visi-
ble to the public as well, so research towards imper-
ceptible secure and robust image watermarking tech-
niques is vital. As mentioned, there are already var-
ious methods that can achieve that, but every single
method requires attention and that’s because we can
not discriminate a specific method as the best. Every
case has its ideal solution and the same idea applies
for image watermarking.
Contribution. In this work we present an efficient
and easily implemented codec system, which we
named WaterIMAGE, for watermarking images that
we are interested in uploading in the web and mak-
380
Chroni M., Fylakis A. and D. Nikolopoulos S..
WATERMARKING IMAGES USING 2D REPRESENTATIONS OF SELF-INVERTING PERMUTATIONS.
DOI: 10.5220/0003936003800385
In Proceedings of the 8th International Conference on Web Information Systems and Technologies (WEBIST-2012), pages 380-385
ISBN: 978-989-8565-08-2
Copyright
c
2012 SCITEPRESS (Science and Technology Publications, Lda.)

ing them public online; this way web users are now
enabled to consider how to protect their own images.
2 BASIC TOOLS
In this section we present basic tools which are used
by our image watermarking system. In particular,
we first describe discrete structures, namely, permuta-
tions, self-inverting permutations, and bitonic permu-
tations, and then briefly outline a codec system (en-
coding/decoding algorithms) which encodes an inte-
ger w into a self-inverting permutation π
∗
and extracts
it from π
∗
. Finally, we propose a 2D representation of
permutations and give a 3D representation of color
images.
2.1 Self-inverting Permutations
Informally, a permutation of a set of objects S is an
arrangement of those objects into a particular order,
while in a formal (mathematical) way a permutation
of a set of objects S is defined as a bijection from S
to itself (i.e., a map S → S for which every element of
S occurs exactly once as image value)(Sedgewick and
Flajolet, 1996; Golumbic, 1980).
Hereafter, we shall say that π
∗
is a permutation
over the set N
9
.
Definition 2.1.1. Let π = (π
1
,π
2
,...,π
n
) be a permu-
tation over the set N
n
, where n > 1. The inverse of the
permutation π is the permutation τ = (q
1
,q
2
,...,q
n
)
with q
π
i
= π
q
i
= i. A self-inverting permutation (or,
for short, SIP) is a permutation that is its own inverse:
π
π
i
= i.
By definition, every permutation has a unique in-
verse, and the inverse of the inverse is the original
permutation. Clearly, a permutation is a SIP (self-
inverting permutation) if and only if all its cycles are
of length 1 or 2; hereafter, we shall denote a 2-cycle as
c = (x,y) and an 1-cycle as c = (x), or, equivalently,
c = (x, x).
The permutation π
∗
= (5,6, 9, 8,1,2,7, 4, 3) is a
SIP with cycles: (1,5), (2,6), (3,9), (4,8), and (7,7).
2.2 Encoding Numbers as SIPs
Next, we present an algorithm for encoding an inte-
ger w into a self-inverting permutation π
∗
and an al-
gorithm for extracting w from π
∗
; both algorithms run
in O(n) time, where n is the length of the binary rep-
resentation of the integer w (author’s algorithms). The
encoding process uses the notion of Bitonic Permuta-
tions which we briefly describe below.
Bitonic Permutations. The key-object in our algo-
rithm for encoding integers as self-inverting permu-
tations is the bitonic permutation: a permutation π =
(π
1
,π
2
,...,π
n
) over the set N
n
is called bitonic if ei-
ther monotonically increases and then monotonically
decreases, or else monotonically decreases and then
monotonically increases. For example, the permuta-
tions π
1
= (1,4,6, 7, 5,3,2) and π
2
= (6,4,3, 1, 2,5,7)
are both bitonic.
Our encoding algorithm uses only bitonic permu-
tations that monotonically increase and then mono-
tonically decrease. Let π be such a bitonic permuta-
tion over the set N
n
and let π
i
, π
i+1
be the two con-
secutive elements of π such that π
i
> π
i+1
. Then,
the sequence X = (π
1
,π
2
,...,π
i
) is called first in-
creasing subsequence of π and the sequence Y =
(π
i+1
,π
i+2
,...,π
n
) is called first decreasing subse-
quence of π.
We next give some notations and terminology
we shall use throughout the encoding and decod-
ing process. Let w be an integer number. We de-
note by B = b
1
b
2
···b
n
the binary representation of
w. If B
1
= b
1
b
2
···b
n
and B
2
= d
1
d
2
···d
m
be two
binary numbers, then the number B
1
||B
2
is the bi-
nary number b
1
b
2
···b
n
d
1
d
2
···d
m
. The binary se-
quence of the number B = b
1
b
2
···b
n
is the sequence
B
∗
= (b
1
,b
2
,...,b
n
) of length n.
Let B = b
1
b
2
···bn be a binary number. Then,
flip(B) = b
′
1
b
′
2
···b
′
n
is the binary number such that
b
′
i
= 0 (1 resp.) if and only if b
i
= 1 (0 resp.),
1 ≤ i ≤ n.
Algorithm W-to-SIP: We briefly outline an algo-
rithm for encoding an integer as self-inverting permu-
tation. Our algorithm, which we call Encode W-to-
SIP, takes as input an integer w, computes the binary
representation b
1
b
2
···b
n
of w, and then produces a
self-inverting permutation π
∗
in O(n) time (Chroni
and Nikolopoulos, 2010).
Algorithm SIP-to-W: Having presented the encod-
ing algorithm Encode W-to-SIP, let us now present
an extraction algorithm, that is, an algorithm for de-
coding a self-inverting permutation. More precisely,
our extraction algorithm, which we call Decode SIP-
to-W, takes as input a self-inverting permutation π
∗
produced by the algorithm Encode W-to-SIP and re-
turns its corresponding integer w. The time complex-
ity of the decode algorithm is also O(n), where n is the
length of the permutation π
∗
(Chroni and Nikolopou-
los, 2010).
2.3 2DM Representations
Given a permutation π over the set N
n
= {1,2,...,n},
WATERMARKINGIMAGESUSING2DREPRESENTATIONSOFSELF-INVERTINGPERMUTATIONS
381
1
2
3
4
5
6
6
5
4
3
2
1
1
2
3 4
5
6
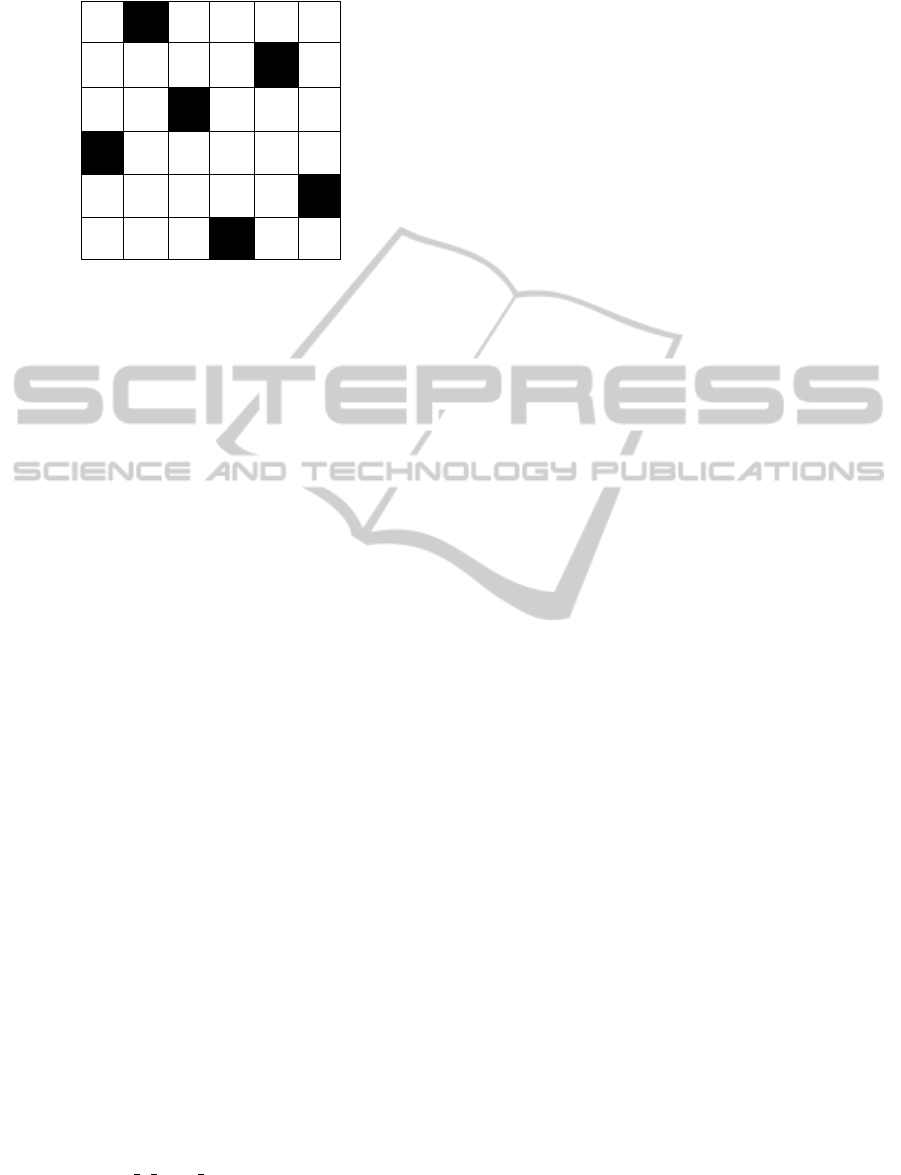
Figure 1: A 2DM representation of the self-inverting per-
mutation π = (5,6,9,8,1,2,7,4,3).
we first define a two-dimensional representation (2D-
representation) of the permutation π that is useful for
studying properties which help us to define, later, a
more suitable representation of π for efficient use in
our watermarking system.
In this representation, the elements of the permu-
tation π = (π
1
,π
2
,...,π
n
) are mapped in specific cells
of an n× n matrix A as follows:
• integer i −→ entry A(π
−1
i
,i)
or, equivalently,
• the cell at row i and column π
i
is labeled by the
number π
i
, for each i = 1,2,...,n.
Based on the previous 2D representation of a per-
mutation, we next propose a two-dimensional marked
representation (2DM representation) of a permutation
which is an efficient tool for watermarking images.
In our 2DM representation, a permutation π over
the set N
n
= {1,2,...,n} is represented by an n × n
matrix A
∗
as follows:
• the cell at row i and column π
i
is marked by a
specific symbol, for each i = 1,2,...,n.
Figure 1 shows the 2DM representation of the permu-
tation π. Note that, as in the 2D representation, there
is also one symbol in each row and in each column of
the matrix A
∗
.
We next present an algorithm which extracts the
permutation π from its 2DM representation matrix.
More precisely, let π be a permutation over N
n
and
let A
∗
be the 2DM representation matrix of π (see,
Figure 1); given the matrix A
∗
, we can easily extract
π from A
∗
in linear time (in the size of matrix A
∗
) by
the following algorithm:
Algorithm Extract π from 2DM
Input: the 2DM representation matrix A
∗
of π;
Output: the permutation π;
1. For each row i of matrix A
∗
, 1 ≤ i ≤ n, do:
find the marked cell and let j be its column;
set π
i
← j;
2. Return the permutation π;
Remark 2.3.1. It is easy to see that the resulting per-
mutation π, after the execution of Step 1, can be taken
by reading the matrix A
∗
from top row to bottom
row and write down the positions of its marked cells.
Since the permutation π is a self-inverting permuta-
tion, its 2D matrix A has the following property:
• A(i, j) = j if π
i
= j, and
• A(i, j) = 0 otherwise, 1 ≤ i, j ≤ n.
Thus, the corresponding matrix A
∗
is symmetric:
• A
∗
(i, j) = A
∗
( j,i) = “mark” if π
i
= j, and
• A
∗
(i, j) = A
∗
( j,i) = 0 otherwise, 1 ≤ i, j ≤ n.
Based on this property, it is also easy to see that the
resulting permutation π can be also taken by reading
the matrix A
∗
from left column to right column and
write down the positions of its marked cells.
2.4 Color Images
A digital image is a numeric representation of a 2-
dimensional image; it has a finite set of values, called
picture elements or pixels, that represent the bright-
ness of a given color at any specific point in the im-
age.
In our system we use the RGB model, where the
name comes from the initials of the three additive col-
ors Red, Green and Blue. The range of colors can be
represented on the Cartesian 3-dimensional system.
The axes x, y and z are used for the red green and
blue color respectively
In our system, since a color is a triple of integers
(x,y,z), a digital image I of resolution N × M (i.e., it
contains N rows and M columns of pixels) is stored in
a three-dimensional matrix Img of size N × M × 3 as
follows:
if the pixel I(i, j) of the image I has (x,y,z)
color, then Img(i, j,1) = x, Img(i, j,2) = y, and
Img(i, j,3) = z.
3 OUR IMAGE WATERMARKING
SYSTEM
Having proposed an efficient method for encoding in-
tegers as self-inverting permutations using the bitonic
property of a permutation, and the 2DM representa-
tion of self-inverting permutations, we next describe
WEBIST2012-8thInternationalConferenceonWebInformationSystemsandTechnologies
382

the two main algorithms of our image watermark-
ing system; the encoding algorithm Encode SIP-to-
IMAGE which encodes a self-inverting permutation
π
∗
, corresponding to watermark w, into an image I
resulting the watermarked image I
w
and the decoding
algorithm Decode IMAGE-to-SIP which extracts the
permutation π
∗
from the image I
w
.
3.1 Embed Watermark into Image
We next describe the algorithm Encode SIP-to-
IMAGE of our codec system which embeds a self-
inverting permutation (SIP) π
∗
into an image I; recall
that, in our system we use a SIP π
∗
over the set N
n
∗
for
encoding the watermark w, where n
∗
= 2n+1 and n is
the length of the binary representation of the integer
w (author’s technique); see, Subsection 2.2.
The algorithm takes as input a SIP π
∗
and an
image I, in which the user wants to embed the
watermark w = π
∗
, and produces the watermarked
image I
w
; it works as follows:
Step 1: The algorithm first computes the 2DM
representation of the permutation π
∗
, that is, it
computes the n
∗
× n
∗
array A (see, Subsection 2.3);
the entry (i, π
∗
i
) of the array A contains the symbol
“*”, 1 ≤ i ≤ n
∗
.
Step 2: Next, the algorithm computes the size N × M
of the input image I and do the following: if N is an
even number it removes the pixels from the bottom
row of I and reduces N by 1, while if M is an even
number it removes the pixels from the right column
of I and reduces M by 1. The resulting image has size
N
∗
× M
∗
, where N
∗
and M
∗
are both odd numbers.
Step 3: Let n
∗
be the size of the SIP π
∗
and let N
∗
≤
M
∗
. Now the algorithm takes the input image I and
places on it an imaginary grid G , which covers almost
the whole image I, having
n
∗
× n
∗
grid-cells C
ij
(I)
each C
ij
(I) of size
⌊N
∗
/n
∗
⌋ × ⌊N
∗
/n
∗
⌋
where, 1 ≤ i, j ≤ n
∗
.
It places the imaginary grid G on I as follows:
it first locates the central pixel P
0
cent
of the image I,
which is at position (⌊N
∗
/2⌋ + 1, ⌊M
∗
/2⌋ + 1), then
locates the central pixel p
0
ii
of the central grid-cell
C
ii
(I), where i = ⌊n
∗
/2⌋ + 1, and places the grid G
on image I such that both P
0
cent
and p
0
ii
have the same
position in I.
Step 4: Then it scans the image and goes to each grid-
cell C
ij
(I) (there are always n
∗
× n
∗
grid-cells in any
image) and locates the central pixel p
0
ij
of the grid-
cell C
ij
(I) and also the four pixels p
1
ij
, p
2
ij
, p
3
ij
, and
p
4
ij
around it, 1 ≤ i, j ≤ n
∗
; hereafter, we shall call
these four pixels cross pixels.
Then, it computes the difference between the
brightness of the central pixel p
0
ij
and the average
brightness of the twelve pixels around it, that is, the
pixels p
ℓ1
ij
, p
ℓ2
ij
, and p
ℓ3
ij
(ℓ = 1, 2,3,4), and stores this
value in the variable dif(p
0
ij
) (see, Figure 2).
Finally, it computes the maximum absolute value
of all n
∗
× n
∗
differences dif(p
0
ij
), 1 ≤ i, j ≤ n
∗
, and
stores it in the variable Maxdif(I).
Step 5: The algorithm goes again to each central pixel
p
0
ij
of each grid-cellC
ij
and if the corresponding entry
A(i, j) contains the symbol “*”, then it increases
• the brightness k
0
ij
of the central pixel p
0
ij
, and
• the brightness k
1
ij
, k
2
ij
, k
3
ij
, and k
4
ij
of its cross pix-
els.
Actually, it first increases the central pixel p
0
ij
by the
value e
0
ij
so that it surpasses the image’s maximum
difference Maxdif(I) by a constant c; that is,
• k
0
ij
+ e
0
ij
= Maxdif(I) + c
and, then, it sets the brightness of the four cross pixels
p
1
ij
, p
2
ij
, p
3
ij
, and p
4
ij
equal to k
0
ij
.
In our system we use c = 5, and thus the bright-
ness k
0
ij
of the central pixel of each grid-cell C
ij
is
increased by e
0
ij
, where
e
0
ij
= Maxdif(I) − k
0
ij
+ 5 (1)
where, 1 ≤ i, j ≤ n
∗
.
Let I
w
be the resulting image after increasing the
brightness of the n
∗
central and the corresponding
cross pixels, with respect to π, of the image I. Here-
after, we call the n
∗
central pixels of I as 2DM-pixels;
recall that, p
0
ij
is a 2DM-pixel if A(i,π
i
) = “*”, or,
equivalently, the cell (i,π
i
) of the matrix A is marked.
Step 6: The algorithm returns the watermarked image
I
w
.
3.2 Extract Watermark from Image
Next we describe our decoding algorithm which is
responsible for extracting the watermark w = π
∗
form
image I
w
. In particular, the algorithm, which we call
Decode IMAGE-to-SIP, takes as input a watermarked
image I
w
and returns the SIP π
∗
which corresponds
to integer watermark w; the steps of the algorithm are
the following:
WATERMARKINGIMAGESUSING2DREPRESENTATIONSOFSELF-INVERTINGPERMUTATIONS
383
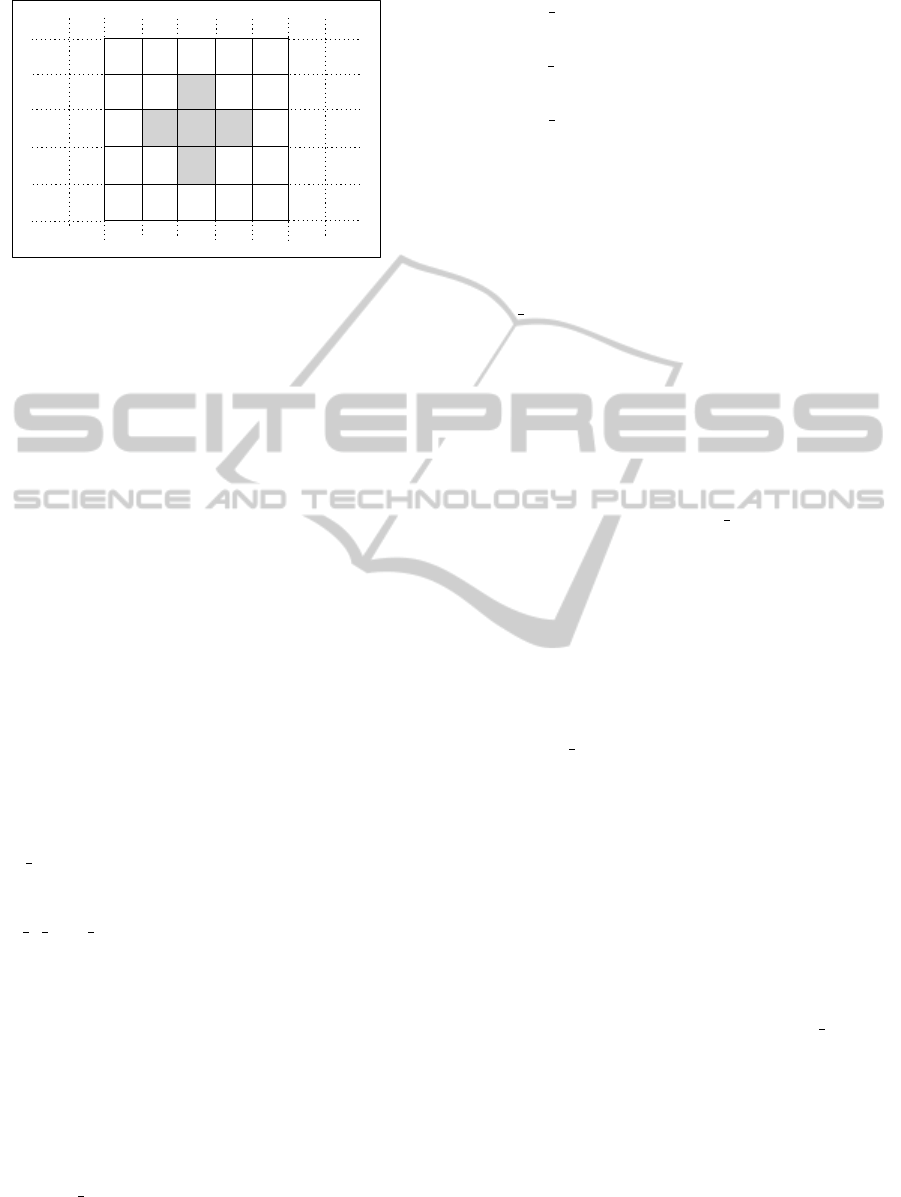
k
2
ij
k
4
ij
C
ij
grid-cell
k
1
ij
k
0
ij
k
3
ij
k
21
ij
k
22
ij
k
23
ij
k
31
ij
k
32
ij
k
33
ij
k
43
ij
k
42
ij
k
41
ij
k
13
ij
k
12
ij
k
11
ij
Figure 2: The brightness k
ℓ
ij
of the central and cross pixels
p
ℓ
ij
of the grid-cell C
ij
(I), 0 ≤ ℓ ≤ 4, and the brightness k
ℓm
ij
of the cycle-cross pixels p
ℓm
ij
, 1 ≤ ℓ ≤ 4 and m = 1,2,3.
Step 1: The algorithm places again the same imagi-
nary n
∗
× n
∗
grid on image I
w
and locates the central
pixel p
0
ij
of each grid-cell C
ij
(I), 1 ≤ i, j ≤ n
∗
; there
are n
∗
× n
∗
central pixels in total. Then, it finds the
n
∗
central pixels p
0
1
, p
0
2
,..., p
0
n
∗
, among the n
∗
× n
∗
,
with the maximum brightness using a known sorting
algorithm (Cormen et al., 2001).
Step 2: In this step, the algorithm takes the n
∗
grid-
cell C
1
,C
2
,...,C
n
∗
of the image I
w
which correspond
to n
∗
central pixels p
0
1
, p
0
2
,..., p
0
n
∗
, and compute an
n
∗
× n
∗
matrix A
∗
as follows:
• Initially, set A
∗
(i, j) ← 0, 1 ≤ i, j ≤ n
∗
;
• For each grid-cell C
m
, 1 ≤ m ≤ n
∗
, do:
if (i, j) is the position of the grid-cell C
m
in the
grid G then set A
∗
(i, j) ← “∗ ”;
It is easy to see that, the n
∗
× n
∗
matrix A
∗
is exactly
the 2DM representation of the self-inverting permu-
tation π
∗
embedded in image I
w
by the algorithm En-
code SIP-to-IMAGE.
Then, the permutation π
∗
can be extracted
from the matrix A
∗
using the algorithm Ex-
tract π from 2DM; see, Subsection 2.3.
Step 3: Finally, the algorithm returns the self-
inverting permutation π
∗
.
4 PERFORMANCE
Our image watermarking system mainly consists of
four algorithms, each of which is responsible for a
particular codec operation:
• Encode W-to-SIP: algorithm for encoding an in-
teger w into a self-inverting permutation π
∗
;
• Decode SIP-to-W: algorithm for extracting w
from π
∗
;
• Encode SIP-to-IMAGE: algorithm for encoding a
self-inverting permutation π
∗
into an integer I;
• Decode IMAGE-to-SIP: algorithm for extracting
π
∗
form the watermarked image;
The two algorithms that are considered the basic ones
for our system are those responsible for embedding a
SIP into an image and extracting the SIP from it.
We next discuss some issues concerning the per-
formance of our image watermarking system. In par-
ticular, we mainly focus on the embedding algorithm
Encode SIP-to-IMAGE and the efficiency of water-
marking image I
w
produced by this algorithm, and
also on important properties of the n
∗
× n
∗
matrix A
∗
which stores the 2DM representation of a SIP. Finally
we show the time and space performance of our sys-
tem by computing the complexity of their algorithms.
It is worth noting that our system incorporates
such properties which allow us to successfully extract
the watermark w from the image I
w
even if the in-
put image I
w
of algorithm Decode IMAGE-to-SIPhas
been compressed with a lossy method and/or rotated.
We have evaluated the embedding and extracting
algorithms by testing them on various and different in
characteristics images that were initially in JPEG for-
mat and we had positive results as the watermark was
successfully extracted at every case even if the image
was converted back into JPEG format. What is more,
the method is open to extensions as the same method
might be used with a different marking procedure part
of the Encode SIP-to-IMAGE algorithm.
All the system’s algorithms have been initially
developed and tested in MATLAB (Gonzalez et al.,
2003) and then redeveloped and also tested in JAVA.
Compression. The experimental results show that the
watermark w is “well hidden” in the image I
w
. We be-
lieve that it is because we mark the image by chang-
ing the difference between the brightness of the 2DM-
pixels p
0
ij
of the n
∗
× n
∗
imaginary grid and its 12
neighborhood pixels around it, that is, the pixels p
ℓ1
ij
,
p
ℓ2
ij
, and p
ℓ3
ij
, for ℓ = 1,2,3,4 (see, Figure 2 and also
Step 2 of the embedding algorithm Encode SIP-to-
IMAGE); recall that, we also set the brightness of the
four cross pixels of each 2DM-pixel p
0
ij
, that is, the
pixels p
1
ij
, p
2
ij
, p
3
ij
, and p
4
ij
, to be equal to the bright-
ness of the 2DM-pixel p
0
ij
.
Note that, we change the brightness of the 2DM-
pixels by increasing them so that they surpass the im-
age’s maximum difference Maxdif(I) by a constant c,
where in our implementation c = 5. We add five be-
cause if we compress the image the values of the pix-
WEBIST2012-8thInternationalConferenceonWebInformationSystemsandTechnologies
384

els may slightly change, and we want our watermark
to be robust. We also believe that this technique de-
spite being simple, it is efficient because the bright-
ness of each of the n
∗
marked central pixels does
not have a great difference from the brightness of the
12 neighborhood pixels and thus the modified central
pixel, along with the cross pixels, does not change
something significantly in the image.
Rotation. The watermarked images produced by our
embedding method have a property worth to be ref-
erenced. And this is certain characteristics noticed
at the 2DM representation of the image’s watermarks
which in our system are self-inverting permutations.
Sometimes an image might show an indeterminate de-
piction, such as a night sky or an aerial view. These
types of images might be rotated changing the coor-
dinates of the watermark’s marks making invalid the
watermark that we are about to extract. Also it is
about an indeterminate depiction which does not al-
low someone to tell which is the right angle of the
image.
Thanks to our embedding method’s properties this
problem can be overcome. It has to do with the co-
ordinates of the marks of a 2DM representation of a
self-inverting permutation found on image I
w
. Those
coordinates allow us to turn the image into the initial
angle and then extract the watermark successfully.
The 2DM representation of a self-inverting per-
mutation has the following properties:
(i) The main diagonal of the n
∗
× n
∗
symmetric ma-
trix A
∗
have always one and only one marked cell,
and
(ii) this marked cell are always in the entries (i,i) of
A
∗
, where i = ⌈
n
∗
2
⌉ + 1,⌈
n
∗
2
⌉ + 2,...,n
∗
.
If the main diagonal of matrix A
∗
has no marked
cell then we rotate the image by 90 degrees. Addition-
ally, if the marked cell of the main diagonal is in entry
(i,i) with i ≤ ⌈
n
∗
2
⌉, then we turn the image by 180 de-
grees and thus we end up at the initial image from
which we are able to extract the right watermark.
Time and Space Complexity. The total time perfor-
mance of our codec system, neglecting the conver-
sion of the input image I into raw raster format, is
N × n
∗
for embedding the watermark w into I and
N + M + (n
∗
× n
∗
) × log(n
∗
× n
∗
) for extracting w
from the watermarked image I
w
. Moreover, the extra
space needed by our codec system is linear in the size
of the input image, i.e., it uses only some extra aux-
iliary variables and an auxiliary matrix for the 2DM
representation of the self-inverting permutation.
5 CONCLUDING REMARKS
In this paper, we proposed a codec system, which we
named WaterIMAGE, for watermarking images that
are intended for online publication.
The proposed WaterIMAGE system has the fol-
lowing design and functional advantages:
• it is an efficient image watermarking system; the
experimental results showed that the watermark w
is “well hidden” in the image I
w
,
• its embeddingmethod incorporates properties that
allow us to successfully extract the watermark w
for the image I
w
even if the image I
w
has been
compressed with a lossy method and/or rotated,
• it is a simple and easily implemented system, and
• finally, as far as the time and space needed for the
encoding/decodingprocess, it performs very well.
We should point out that the main feature of our Wa-
terIMAGE system is the fact that it uses a combina-
torial object to watermark an image; we show that
an integer can be efficiently represented by a self-
inverting permutation which, in turn, can be repre-
sented in the 2-dimensional space and, thus, this rep-
resentation forms a suitable watermarking object for
images. In our system we propose a marking method
but apart from that the investigation of alternative and
more efficient methods for marking an image using a
2D representation of a permutation are an open prob-
lem for further research.
REFERENCES
Chroni, M. and Nikolopoulos, S. (2010). Encoding water-
mark integers as self-inverting permutations. In Proc.
Int'l Conference on Computer Systems and Tech-
nologies (CompSysTech'10), volume ACM ICPS 471,
pages 125 – 130.
Collberg, C. and Nagra, J. (2010). Surreptitious Software.
Addison-Wesley.
Cormen, T., Leiserson, C., Rivest, R., and Stein, C. (2001).
Introduction to Algorithms. MIT Press, 2nd edition.
Garfinkel, S. (2001). Web Security, Privacy and Commerce.
O’Reilly, 2nd edition.
Golumbic, M. (1980). Algorithmic Graph Theory and Per-
fect Graphs. Academic Press, Inc., New York.
Gonzalez, R. C., Woods, R. E., and Eddins, S. L. (2003).
Digital Image Processing using Matlab. Prentice-
Hall.
Sedgewick, R. and Flajolet, P. (1996). An Introduction to
the Analysis of Algorithms. Addison-Wesley.
WATERMARKINGIMAGESUSING2DREPRESENTATIONSOFSELF-INVERTINGPERMUTATIONS
385
